WHY CHOOSE COMET BACKUP FOR ON-PREMISES BACKUP?
Complete Data Ownership and Control
Keep your backup data fully on-site and under your control. Store backups on your own servers, NAS, SAN, or private infrastructure without relying on third-party cloud providers. You decide where data lives, how it's secured, and who can access it.
No Vendor Lock-In
Use your existing hardware and storage infrastructure without being tied to a specific cloud vendor or recurring storage markup. Scale storage on your own terms and integrate with your current IT environment without forced migrations.
High-Performance Local Recovery
Restore data at LAN speed directly from your on-premise storage. Large file recoveries, full system restores, and disaster recovery operations complete faster without cloud latency or bandwidth bottlenecks, or egress fees.
Secure, Encrypted, and Compliant
All backups are encrypted with AES-256 military-grade encryption before leaving the workstation or server, and you retain full control of encryption keys. Combine on-premise storage with role-based access controls, MFA, and IP allowlisting to restrict administrative access to trusted networks.
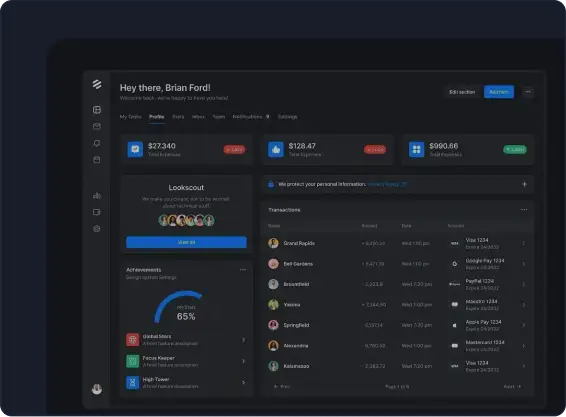
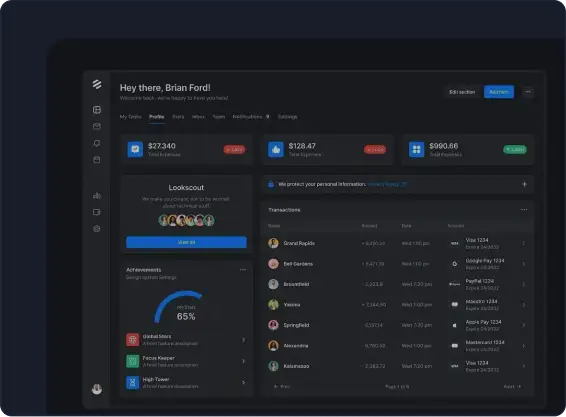
WATCH IT IN ACTION
See how easy it is to set up and recover your data in this short demo.
POWERFUL ON-PREMISE BACKUP FEATURES FOR MAXIMUM CONTROL
DESIGNED FOR SECURITY & CONTROL
MSP Service Delivery
Build profitable backup services using your own infrastructure with complete margin control, faster local restores, and customer data remaining in your controlled environment.
Enterprise Data Protection
Protect critical business data within corporate data centers, enabling branch office consolidation, air-gapped security, and compliance boundary enforcement.
Hybrid Cloud Strategies
Combine on-premise performance with cloud durability. Hot data stays local for fast access while cold data archives to cloud for offsite redundancy and long-term retention.
FAQS
Most deployments are operational within 15-30 minutes. For direct-to-storage configurations, simply install the backup agent and configure the storage path. Storage Gateway deployments require installing the backup agent on your server, after which you can provision customer vaults through the centralized management console. Large environments can use seed loading to bypass initial upload delays.
Comet Backup supports local filesystem paths (Windows, Linux, macOS), SMB network shares for NAS integration, SFTP servers for secure Linux-based storage, and FTP as a legacy option. The Storage Gateway architecture transforms any of these into scalable, multi-tenant object storage with S3-compatible APIs, enabling hybrid cloud configurations with centralized management.
Yes. The Storage Gateway architecture is specifically designed for scale, supporting thousands of servers and endpoints through isolated buckets, unique authorization keys per vault, and automated provisioning. The system handles multi-threaded operations, intelligent load balancing, and spanned storage across multiple disks, making it ideal for MSPs, large organizations with multiple locations or franchises.
Unlike cloud-only backup vendors that require you to store data in their infrastructure, Comet Backup lets you deploy fully on-premises and store backups on your own servers, NAS, or private storage. You maintain complete control over your data location, security policies, and retention strategy without vendor lock-in or forced cloud storage markups.
Comet Backup allows you to use your own on-premises storage hardware and infrastructure, eliminating dependency on a single storage provider. You can scale using your existing environment, migrate storage as needed, and maintain full ownership of your backup data at all times.
Yes. Comet Backup enables LAN speed backup and restore directly from your on-premises storage. Large file restores, full system recoveries, and disaster recovery scenarios complete quickly without cloud latency, bandwidth limits, or egress fees slowing you down.
Absolutely. Comet Backup allows you to use on-premises storage as your primary backup destination while simultaneously replicating to cloud or offsite storage. This flexibility enables a true 3-2-1 backup strategy for redundancy, disaster recovery, and ransomware resilience without changing platforms.


